I've Made Another Virus!
Ok, I have a lot of issues with AV software blocking genuinely .exe files from executing, but today I’ve made a really simple utility for myself - urlong. I mean, it’s really simple - you provide it with a shortened URL and it prints out long form.
The utility simply queries passed URL and follows 301: Moved Permanently HTTP response code until reaching the end of it. Here is full source code of it:
#include <iostream>
#include <cpr/cpr.h>
using namespace std;
int main(int argc, char* argv[]) {
if(argc < 2 || string(argv[1]) == "-h") {
cout << "url longener v" << APP_VERSION << " (" << APP_GITHUB_URL << ")" << endl;
cout << "usage: urlong <url>" << endl;
return 1;
}
string url = argv[1];
while(true) {
cpr::Response r = cpr::Get(cpr::Url{url}, cpr::Redirect{false});
if(r.status_code == 200) {
cout << url << endl;
return 0;
}
if(r.status_code == 301) {
url = r.header["Location"];
} else {
cerr << "failed: " << r.reason << endl;
}
}
return 0;
}
Now, uploading to VirusTotal gives absolutely shit results:
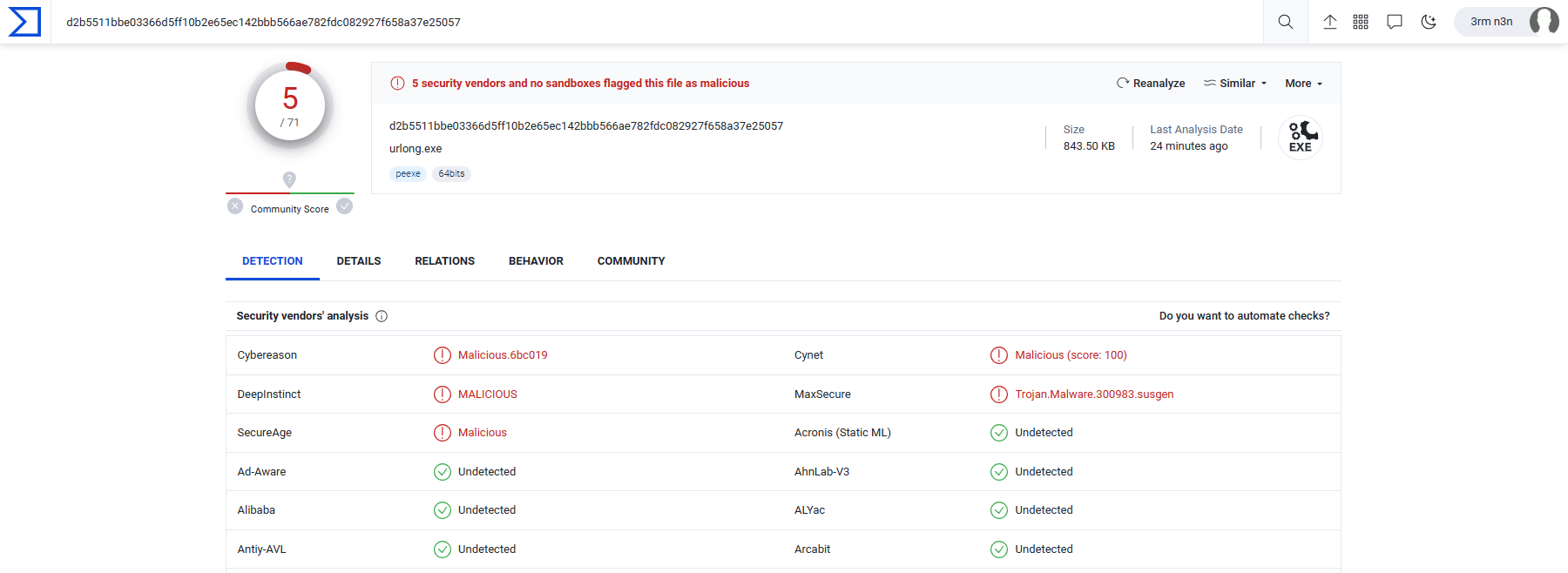
Apparently, 5 out of 71 AV think that this util is either malicious or a trojan. Really?
I’m thinking now, do antiviruses actually do anything useful at all? Ok, they might protect from something but is this like 10% or 20% of threats, or how much? They say, antivirus software can be effective against a significant portion of known and common threats, but what is significant in numbers? Significant to who? An attacker? A user?
Digging deeper, this is what googling has to say:
it is still possible for false positives to occur, especially in situations involving less common or unrecognized software, custom-coded applications, or complex system configurations. Additionally, the sensitivity settings of the antivirus program can also impact the occurrence of false positives. Higher sensitivity levels may lead to more false positives but can provide stronger protection against unknown threats.
To minimize the impact of false positives, antivirus software typically provides options for users to manage and customize the scanning settings. These settings allow users to exclude trusted files, folders, or programs from scans, adjust sensitivity levels, or set up whitelists for known safe software.
If you find that a particular antivirus program consistently generates excessive false positives or is incompatible with your specific needs, you may consider exploring alternative antivirus solutions that better suit your requirements. It’s worth noting that different antivirus programs have different detection rates and may vary in their handling of false positives.
Or, in other words, this is what antivirus software key functions are in the realm of cybersecurity:
- Verification of Authentic Software. Antivirus software possesses knowledge of prominent, widely-used software applications and has the capability to discern whether the installed version corresponds to the original, unaltered copy. This ensures the integrity of recognized, reputable software packages. Note that only big, old, expensive, and commercial software falls under this definition.
- False Positive Reporting. However, when encountering lesser-known or customized software, the likelihood of generating false positives significantly increases. These false positives entail instances where the antivirus program mistakenly identifies legitimate software as potentially malicious. In such cases, it becomes necessary for users to manually exclude the specific software from future scans.
I hope this post has clarified the objectives and benefits of AV, as I have learned a lot from this project. AV is not a silver bullet, but a pretty weak cybersecurity tool that simply has too much press and noise around it. Thank you for your attention and feedback.
To contact me, send an email anytime or leave a comment below.
