Discovering Chrome(ium) Profiles on Windows PC
At the moment BT discovers Chromium profiles by going into %APPDATA%/Local/.../User Data folder and enumerating subfolders which are either called Default or start with Profile.
Then it goes into each of those folders and reads a JSON file called Preferences to extract human readable profile name.
And this is OK, unless a user has tons of profiles, and reading JSON files is also a lengthy process due to how large those Preferences files are!
Improvements
There is a better/faster/more secure (not the most secure) way to list profiles in Chromium by just reading file %APPDATA%/Local/.../User Data/Local State which is also a JSON file, and contains profile property, which has info_cache property, under which all the profiles are listed.
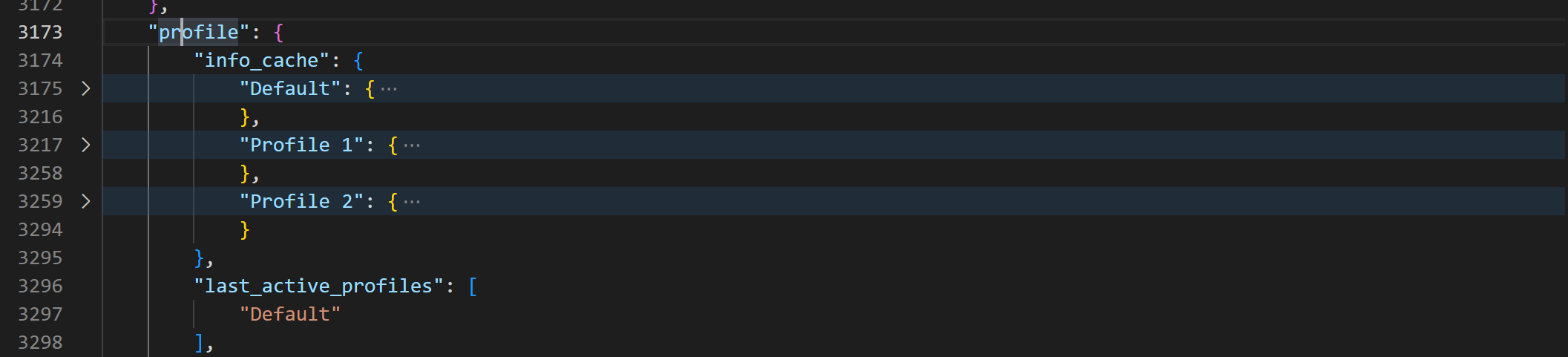
Each profile object has shortcut_name property, which in turn contains human readable name of the profile, and that’s exactly what Browser Tamer is using to display those.
Unfortunately, this method is still reading a file from your user data directory of a Chromium browser, but now it’s just a single file read instead of many. This still may trigger anti-virus alerts, but at the time of this writing there is no other safe way to enumerate profiles.
P.S. Browser Tamer is a browser automation system utility done in spare time by myself. Official page is located here.
To contact me, send an email anytime or leave a comment below.
